No Internet of Things without strong cyber security

The concept of IoT holds great potential: By connecting millions of devices to the internet we can save time and money and become more efficient, we can offer our customers more convenience, better service and much more. But no grand vision without a snake pit of problems: With the Internet of Things comes the Internet of Threats. We need to protect our new network-aware systems and devices. There will be no Internet of Things without a strong focus on cyber security.
Some security experts compare the current state of IoT security with Asbestos. They predict that in a few years time we’ll look back asking ourselves “What were we thinking of?”. Others draw parallels to the World Wide Web of 1994-95, arguing that IoT will be a security train wreck for years, before we eventually figure it out.
Messages like these may paint a too gloomy picture of the challenges within IoT. But nevertheless, cyber security is a crucial IoT prerequisite, not least due to its close interaction with the physical world. IoT threats can go far beyond the well-known, conventional Internet threats like credit card theft. They could disable home security systems, manipulate navigation systems on connected vehicles, disrupt smart medical devices or knock out entire energy systems.
IoT is speeding up
At Data Respons we have broad experience and a long track record in IoT security, and currently we are experiencing a significant increase in customer inquiries and projects in the IoT cyber security domain.
No wonder, because IoT is coming at us with terrific speed. We are connecting more and more devices and systems to the Internet, whether they’re industrial control systems, cars, cameras, door locks, fitness trackers or medical technology. By 2020, the number of installed IoT devices is forecast to grow to nearly 31 billion worldwide. And IoT threats are increasing simultaneously: Experts predict that in 2020 more than 25 per cent of enterprise attacks will involve IoT.
Increasing awareness
Luckily, awareness of the importance of IoT security is increasing. For instance, it was a wake-up call for the IoT business, when in 2016 the Mirai botnet succeeded in enslaving millions of devices, including IP cameras and routers, turning them into centrally controlled botnets for Distributed Denial of Service (DDoS) attacks. Currently there are still Miria variants, like Mukashi, out there constantly scanning the web for vulnerable IoT devices, looking for weakly protected machines with factory-default credentials or common passwords.
Moreover, in June 2020 the largest independent consumer body in the UK, Which?, revealed that 3.5 million cheap wireless cameras produced in China and distributed worldwide could potentially be hijacked by hackers.
New security agenda
So, the picture is quite clear: IoT sets a whole new agenda for cyber security. It’s not enough to take security concepts and standards from the world of modern administrative IT and adapt them to this new domain. Furthermore we have to keep in mind the closeness of IoT to the physical world, together with the increased complexity and multi-layer nature of many IoT ecosystems. All this requires a multi-level approach to security.
For the sake of clarity let’s divide IoT projects into two different categories, each of which requires different approaches: Firstly, developing a complete new IoT product from scratch, and secondly, adapting a legacy system to the new world of IoT.
Greenfield projects
Developing new IoT products is relatively straightforward, seen from a security perspective. Starting from scratch gives you the advantage of incorporating security into an early stage of your design. You can do security-by-default, taking all the right decisions when it comes to patches, updates, access control, user authentication etc., integrating security from the very beginning.
Also, greenfield projects allow you to adopt a holistic security approach. Thinking holistically is the best way to handle the complexity of the multi-layer IoT ecosystem. It means thinking security on every level, whether it is on the sensor/actuator and gateway level, whether it is encrypting the data sent through the system, or securing the stored data and the web and mobile applications being developed.
Risk assessment
Another important approach is risk assessment. It helps you channel your security effort into where it’s most needed and where it will make the biggest difference. Risk assessment means finding vulnerabilities and threats, estimating the likelihood of the threat to become reality, finding ways to mitigate attacks etc.
It is crucial that risk assessment is done for the complete end-to-end value chain of an IoT product or service, bearing in mind that it’s more complex than conventional digital services. An IoT solution will typically be blending technologies, devices, software, connectivity, data storage etc., so there is much to consider. For instance, you may have designed an IoT device with great security features. But if you fail to think security when you’re designing the app associated to it, you might get in trouble. Likewise, if there are flaws in the cloud solution you have chosen to store your data.
Risk assessment is increasingly gaining momentum, driven among other things by standards and legislation requiring developers to take a holistic, risk-based approach to IoT security. Furthermore, this approach helps you prioritize your development resources and helps you spend your security budget where it makes the biggest difference.
Legacy systems
A whole new challenge comes, when we want to adapt older systems to the modern IoT world. Bringing systems developed 20 or 30 years ago into the new world of IoT requires much consideration regarding security.
Quite understandably the companies responsible for these systems want to give their customers access to the new business opportunities coming from IoT. As an example, manufacturers of ship engines and other heavy duty ship equipment are looking for ways to bring their machinery online, thus creating new possibilities for service and maintenance. But enabling these legacy systems in terms of access and connectivity to the internet from everywhere and from a wide range of devices means exposing them to a new world of security risks. Connecting to the Internet means connecting to potential cyber threats.
Low level of security
This is particularly challenging, as these legacy systems are “born” with a very low level of security, both in terms of the way they have been developed and the way they are maintained. Now they have to be aligned to the modern cyber security world, and to meet state-of-the-art requirements for patching, updates, password protection etc. That is a major challenge.
Probably the companies responsible for these legacy systems are not in the habit of issuing security patches, simply because they have never been required to do so. Patches were released, when there was a requirement for e.g. new functionality.
Making legacy systems that were never intended to work with any kind of security, comply with modern security requirements is a complex task. But it has to be done, because all the advantages coming from connectedness will turn into threats, if we are unable to ensure the confidentiality, integrity and availability of these systems.
IoT vulnerabilities
Patching
Patches are not released with the same frequency as commonly done in the IT world. That leaves vulnerabilities in the system for a long time before patches are sent out to fix the problem. Or worse: Some devices are not designed to receive patches/updates at all
Weak Passwords
Some IoT devices have only 4, 5 or 6 digit passwords, and this lack of complexity means they are easily breakable. Also, it may not be possible to change the admin user of the device, and default usernames and passwords are easy to find on the Internet.
Communication
Is communication from the device encrypted, and if yes, is encryption strong enough? Is it encrypted both in transit and in rest?
Faulty software
When you develop your IoT product it may be a good idea to reuse software developed by others. However you have to check that the software you’re reusing is without security flaws, and that you’re using the newest version of the code.
End-of-life
What happens if the component or device you’re using reaches end-of-life and is not supported by the supplier anymore?
Privacy protection
Do you have any data about your user stored on the device? What about 3rd party integrations?
Only one layer of security
One layer is not enough. You need defence in depth, where several layers of security are used to protect data and information
The need for security standards
The vast majority of IoT devices or devices used in ICS (Industrial Control Systems) do not follow or have not been designed to follow security standards or guideline. This means that we’ll need to “pave the road while we drive it” i.e. design and implement security during the implementation, instead of during the design of the products or early in the products’ lifecycle.
Some security standards exist though, like IEC 62443. Others are about to be developed on a European level e.g. from ENISA (The European Union Agency for Cybersecurity) and ISO (International Standardization Organization). These will become available in the years to come.
More pro-activity needed
Luckily, awareness regarding cyber security is rising. The media is publishing cyber crime stories on an almost daily basis, and manufacturers and service providers face considerable pressure from both customers and from governments and regulators, if they are found neglecting their security responsibilities.
But still we see more reactivity than pro-activity. All too often security experts or tech-savvy users are the ones that find and publish security flaws. Only then manufacturers will fix the problem, and by that time the damage done could be significant.
In the coming years we will be witnessing numerous incidents, in which IoT devices are used for cyber attacks or in which customer data has been compromised. The companies affected will react in retrospect, but ideally it should be the other way around: Because of high security standards and heightened awareness we will – hopefully soon – get to a point, where reacting in retrospect is rare and where heightened awareness will keep incidents to a minimum.
Well-known dilemma
However, the well-known dilemma between convenience and security will continue to challenge companies, developers as well as cyber security experts. The old saying about password complexity also applies to IoT security: the longer and more complex, the more secure, but the more tiresome as well.
On the one hand companies and customers want convenience and ease-of-use. They want devices and services available at their fingertips without the hassle of security procedures. On the other hand we have the security experts pushing for confidentiality, integrity and availability. The tricky thing is to find the balance between these two considerations.
But when you consider this dilemma more closely, you’ll find that there is no getting around security. In fact, although the starting point for many companies in IoT is the cost savings and convenience IoT has to offer, they quickly realize that only with security in place they can focus back on realising the potential of IoT, optimizing processes, boosting service, reducing costs and designing outstanding customer experience.
Stay Connected
Everything On Graal VM
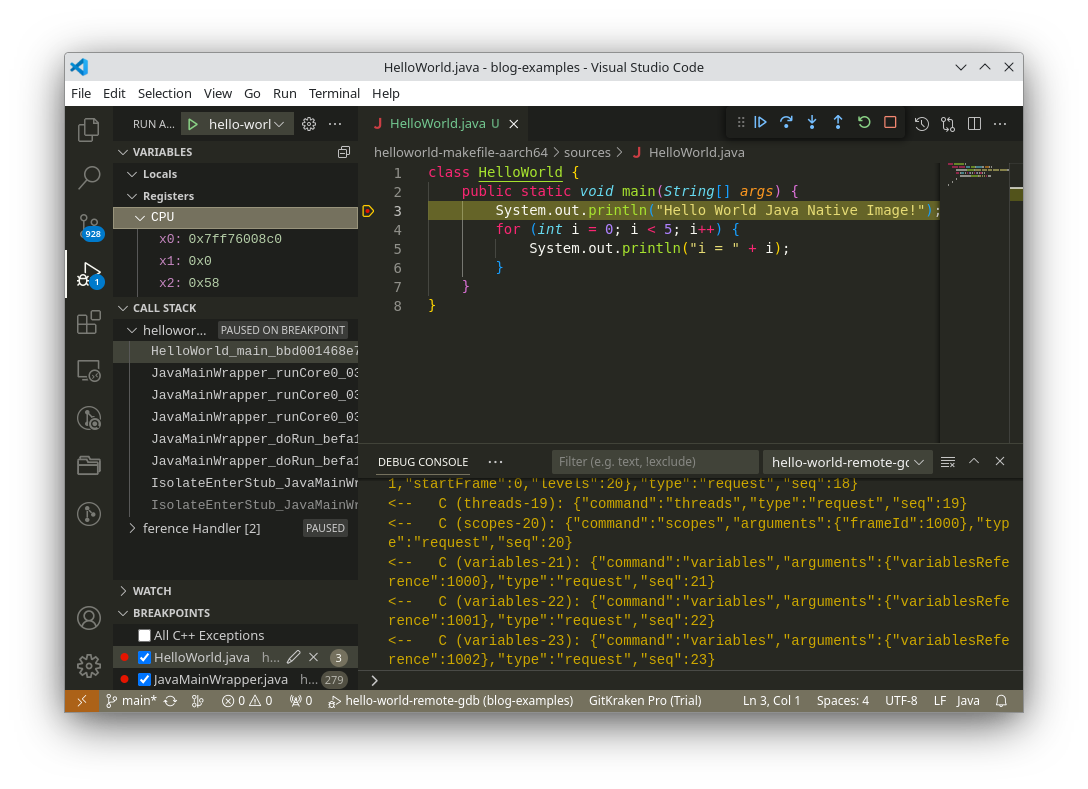
We illustrate how to build and debug the native image of a Java application, produced by MicroDoc GraalVM Embedded, and running on a remote embedded device. The debugging experience is illustrated inside the VSCode IDE. The embedded device runs Linux on an ARMv8-A processor (running in AArch64 mode), like a RaspberryPi 4 or 5.

For devices that are not powerful enough to run a full feature browser or Android system, MicroDoc is developing a user interface framework directly integrated with the Graal virtual machine. Why? Because the number of small devices is increasing dramatically, and although they may be small and low powered they still deserve an up-to-date user interface.

Would it be fair to say that the GraalVM is a step closer to the holy grail of polyglot programming? Yes, according to the virtual machine experts from MicroDoc. Here’s an overview of what the GraalVM can do for software developers.
